Cloud computing is growing at an unprecedented rate, and it is estimated that cloud services will reach a global market value of $411 billion annually by 2020 with annual growth exceeding 15 per cent (Columbus 2019; Gartner 2019). Cloud computing services allow businesses the flexibility of accessing data storage and software resources according to their needs without costly investments in technology hardware. However, users are concerned that providers will use their data in unwanted ways and that their data will be compromised through hacker attacks. Such concerns are not unfounded, as attacks on cloud data have been all too common in recent history. For example, Dropbox, a file sharing cloud service provider, experienced data breaches in 2012 that resulted in the exposure and posting for sale of millions of users’ login information on the dark web (Turner 2016). In 2014, hackers illegally accessed and exposed numerous celebrities’ private photos stored on Apple’s cloud service, iCloud (Lewis 2014). Recently, more than 200,000 CVs originating from two online recruiting firms were exposed after hacking attacks on their cloud storage service (Yahoo News 2019). Such data breaches highlight the importance of understanding the measures cloud providers have in place for data privacy and security before rushing into the cloud.
Privacy policies are the primary means by which online service providers communicate their data privacy and security practices with users. If such policies are to be successful in reassuring and attracting potential users, it is critical that they provide adequate content and present this content in a manner that enables users to fully resolve their concerns. We examined 50 cloud service providers’ privacy policies, focusing on the types of content provided and how this content is conveyed to users with an analysis of the linguistic characteristics of the policies (i.e., readability, the use of language indicating uncertainty, and use of positive or negative linguistic tone). Our results identify current practices and areas of weakness in cloud privacy policy design.
First, we examined what policies say about the information that is collected and its disclosure. Results indicate that cloud service providers commonly collect details about the users themselves (e.g., their names and addresses), server logs or cookies, details about the services being provided, and details about users’ mobile devices. Most of the policies we examined (81 per cent) state that they disclose information to third-party business partners. Information is also commonly disclosed to a third-party if there is a merger or acquisition or if there is a law enforcement request or court order.
But what do policies say about data security and integrity measures? Figure 1 presents the five major types of content contained in privacy policies and percentage of words dedicated to each area. This analysis reveals that a surprisingly limited proportion of privacy policy content (9.7 percent on average) is devoted to describing the measures for data security and integrity. While most privacy policies provide a general statement indicating they will protect the security and privacy of the data, few providers provide assurance by listing specific protection measures, such as data encryption and/or firewalls. Of further concern, only 2 per cent of the providers we examined stated that they ask third-party auditors to verify their security practices. Finally, while most of the providers (81 per cent) state that they will disclose users’ data to business partners, only 28 per cent require their business partners to have similar privacy and security measures.
Figure 1. Percentage of words in each content category
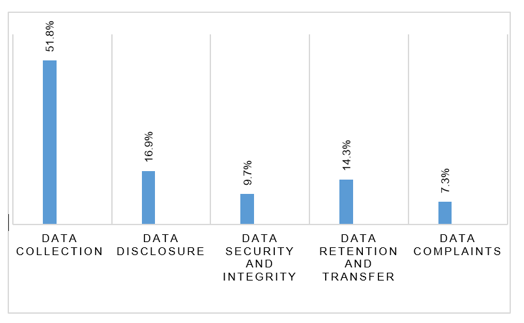
Policies may also address what happens to data after users terminate service, what information is provided about data transfer, and what procedures are in place for complaints. Slightly more than half of the policies examined included detailed data retention procedures describing what happens to data in the cloud if customers decide to terminate the service. In terms of data transfer, several frameworks exist that outline methods for companies to transfer personal data between countries in a manner that is consistent with relevant laws. Our results indicate that 68 per cent of the providers indicate that they follow U.S./EU and U.S./Swiss frameworks for transferring data, while only 4 per cent indicate that they follow the Asia Pacific Economic Cooperation (APEC) framework. Most cloud service providers list contact information for clients to use for reporting data concerns and complaints. However, very few providers explain what actions they will take or their process for investigating and responding to reported concerns.
We next examined the linguistic characteristics of privacy policies to understand whether cloud providers are effectively conveying the content in the policies. Figure 2 illustrates the observed readability across the five content areas based on the Flesch Reading Ease scale, where a higher score (out of 100) indicates greater readability. Overall, the readability analysis indicates that cloud service providers’ privacy policies are overly difficult to read, especially when describing data security and integrity measures and procedures for data retention and transfer.
In privacy policies, an abundance of words associated with uncertainty (e.g., indefinitely, maybe, occasionally, possibly, etc.) may give readers the impression, whether warranted or not, that the cloud service provider is not confident in its ability to protect users’ private information. We find the highest occurrence of uncertainty words in sections of policies describing the disclosure of users’ information, which may amplify users’ concerns about who will have access to their data and where their information will be disclosed.
Figure 2. Readability in each content category

In summary, cloud service users, particularly business users who are examining contractual relationships, may use this study to assess the relative strengths and weaknesses of a potential service provider’s privacy policy. For cloud providers, this research identifies several areas where improvements in policy content and language are warranted, such as additional content related to all aspects of data safety and integrity measures, increased discussion of how companies act in response to reported concerns, and a general need to improve the readability of language across all content areas.
♣♣♣
Notes:
- This blog post is based on the authors’ paper A Content Analysis of the Privacy Policies of Cloud Computing Services. Journal of Information Systems, in press.
- The post gives the views of its author(s), not the position of LSE Business Review or the London School of Economics.
- Featured image by Blue Coat Photos, under a CC-BY-SA-2.0 licence
- When you comment, you’re agreeing to our Comment Policy
 Lei Gao is an assistant professor of accounting at the University of Akron where he has been a faculty member since 2017. Lei completed his Ph.D. at Virginia Commonwealth University and his master’s degree of accounting and information systems at Virginia Tech. His research interests lie in the area of judgment and decision-making in accounting, ethics and fraud, and the role of technology in accounting information disclosure.
Lei Gao is an assistant professor of accounting at the University of Akron where he has been a faculty member since 2017. Lei completed his Ph.D. at Virginia Commonwealth University and his master’s degree of accounting and information systems at Virginia Tech. His research interests lie in the area of judgment and decision-making in accounting, ethics and fraud, and the role of technology in accounting information disclosure.
 Alisa G. Brink is the KPMG Teaching Excellence professor in the department of accounting at Virginia Commonwealth University. She teaches courses in financial accounting and experimental accounting research. Dr. Brink’s primary research interests include judgment and decision making in managerial and financial accounting. Her specific research topics of interest include creativity, incentive framing, participative budgeting, whistleblowing, and accounting education.
Alisa G. Brink is the KPMG Teaching Excellence professor in the department of accounting at Virginia Commonwealth University. She teaches courses in financial accounting and experimental accounting research. Dr. Brink’s primary research interests include judgment and decision making in managerial and financial accounting. Her specific research topics of interest include creativity, incentive framing, participative budgeting, whistleblowing, and accounting education.